Cloud Hosting
Best practice tips for better cloud security [Part 1]
![Best practice tips for better cloud security [Part 1]](https://www.storminternet.co.uk/app/uploads/2023/03/cloud-security-concept.jpg)
By 2025 cybercrime may cost the world as much as $10.5 trillion per year, giving it a GDP second only to America and China. But by implementing cloud security best practices and tools you may be able to avoid becoming part of a statistic that estimates that 99% of security breaches in 2025 will be down to mistakes made by businesses rather than their cloud service providers (CSP).
These mistakes are broadly due to businesses not understanding their role in the shared responsibility model, which then results in misconfigurations and omissions. The emphasis is on the shared responsibility model that details those security responsibilities belonging to the CSP and the customer respectively.
According to the National Cyber Security Centre (NCSC), basic responsibility can be allocated using cloud service models as a reference:
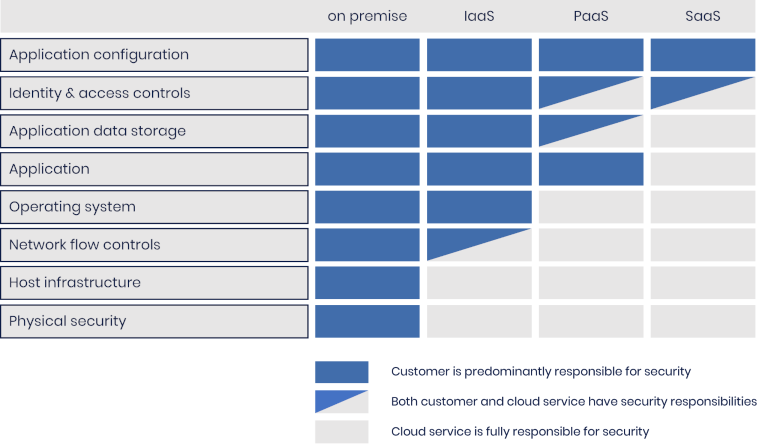
Source: National Cyber Security Centre
The table above is, however, more of a guideline than an actual allocation of responsibility. With managed services, for example, the CSP might assume additional responsibility with regard to the customer’s cloud security. It is up to you, the customer, to discuss the division of security responsibilities with your cloud service provider.
Even when a complete cloud security profile has been mapped out, following cloud security best practices is an essential part of being online, and can help you from becoming part of a statistic.
Keep track of your cloud assets
In a previous post, we briefly touched on the topic of cloud cost overrun, referring to workloads that ran year-round without any type of cost oversight, causing you to blow through your cloud budget sooner than expected. Embedded in that concept are ‘forgotten’ cloud assets like virtual machines initially used for testing but serve no current purpose.
This is formally referred to as ‘VM sprawl’ or, in a broader context, ‘virtualisation sprawl’ and can be a crucial security risk, especially as cloud environments are becoming increasingly complex and therefore more difficult to monitor and manage. Such forgotten infrastructure can also cause compliance issues if sensitive information is stored on it.
When virtualisation sprawl occurs, it can provide attackers access to the network without being detected.
Create and enforce robust IAM policies and systems
Seeing users with passwords like `Password!’ can send chills through any sysadmin’s veins – which it does, because they are more common than you might think. Passwords are, however, only a small part of Identity and Access Management, or IAM.
IAM refers to an ecosystem of business policies and processes and the technologies which enable their execution. IAM determines who can gain access to systems (authentication), who can access specific resources in those systems (authorisation), and with which technologies authentication and authorization are managed.
Given that entry to a network is controlled by IAM systems, such systems are often the primary targets of attacks. It’s therefore important to:
- Be clear about who creates access rules (IT vs management)
- Secure IAM platforms and implement monitoring policies
- Realise the risks inherent to a centralised IAM platform which, when breached, provides access to your entire infrastructure
- Enforce policy-based implementation of authentication and authorization
- Use automation for repetitive tasks to reduce the potential for human error
- Employ multi-factor authentication (MFA) methods across all endpoints (such as servers, laptops, mobiles, etc.)
At the same time, it’s important to ensure that only relevant systems and information are accessible and that everything else is safely stored elsewhere.
Perform regular penetration testing
Admittedly, the problem with posts like this one is that the cloud security best practices are broad, and sometimes difficult to implement. This is where penetration testing, or ‘pen testing’ becomes invaluable since it can pinpoint specific security issues and policy shortcomings with greater accuracy. When pen testing is performed on a periodic basis, your organisation stands a better chance of weathering emerging threats.
There are three flavours of pen testing:
Black box testing
Black box testing essentially simulates a real external attack on the network. The attacker doesn’t have access to your system and has little to no knowledge of the internal workings of the IT infrastructure. The goal here is to gain access to your organisation’s cloud infrastructure.
White box testing
At the other end of the spectrum is white box testing, where pen testers have full access to your IT infrastructure. White box testing is perhaps more akin to an in-depth security audit to identify all possible attack vectors and can include meticulous code and application analyses.
Grey box testing
Neatly positioned in the middle is grey box testing. The pen tester often starts with valid credentials which will allow access to the IT infrastructure and attempts to escalate privilege to access more sensitive information and systems.
Of the three, grey box testing is the most popular since it incorporates aspects from the other two. It’s also more cost-effective for smaller organisations (pen testing can be expensive). However, all three methods of pen testing can be incorporated into a multi-year strategy to create a highly robust and secure cloud environment. It’s worth noting that pen testing is a PCI DSS certification requirement.
Create a Business Continuity and Disaster Recovery (BCDR) Plan
A robust cloud security strategy shouldn’t just focus on preventative measures, but should also include planning that mitigates data loss and downtime in a disaster scenario. Disaster scenarios aren’t just limited to natural disasters, but also online attacks (e.g. ransomware) as well as human error.
Business continuity in this case refers to how an organisation reacts to incidents to ensure a minimum level of operation in such an event. Disaster recovery, on the other hand, refers to the actions required to return the business to a normal state of operation. Both concepts are very closely related and often overlap.
There are several crucial ingredients to an effective BCDR strategy:
Infrastructure audit
A complete audit of all systems, users, hardware, and software is often a good starting point to develop your BCDR strategy. This can also provide insight into possible virtualisation sprawl and so reveal potential security risks to your organisation’s cloud infrastructure.
Risk assessment
A risk assessment includes examining scenarios that can lead to data loss or loss of access to critical cloud-based systems. It’s equally important to assess the impact scenarios where these risks are realised and so determine the cases in which a BCDR strategy will be necessary.
Disaster mitigation
Now that potential risks and their impact have been identified, a recovery strategy can be developed. Each risk within the risk assessment can be evaluated and assigned its own recovery strategy. This should include backups and redundant failover infrastructure that can ensure continuity. At the same time, key role players in such a disaster scenario should also be identified / assigned.
Test, test, test!
Simulating a disaster scenario evaluates your BCDR for efficiency, and will help identify shortcomings. Testing can optionally be combined with penetration testing to stress-test your BCDR strategies.
Wrapping up
Cloud security is a broad and continuous process, which can be simplified by adhering to established best practices. An audit of your cloud infrastructure is a good start and could reveal infrastructure you may have overlooked. At the same time, knowing which security measures are your responsibility and which are those of your cloud service provider can help pinpoint holes in your existing security. Identity and access management (IAM) helps determine who has access to your infrastructure, and what they can access. But running a centralised IAM system can make you more vulnerable to attacks, which is why pen testing is crucial to your cloud security. Regardless of the size of your infrastructure, business continuity and disaster recovery is vital and will be the difference between life and death for your organisation in the event of a breach.
Speak with a Storm Expert
Please leave us your details and we'll be in touch shortly
A Trusted Partner








