Distributed Denial of Service (DDoS) attacks are among the most notorious and potentially devastating types of cyber attacks. The premise behind such an attack is straightforward: it involves overwhelming a target’s network or servers with an immense volume of traffic, to the point where its security mechanisms fail or the service becomes inaccessible.
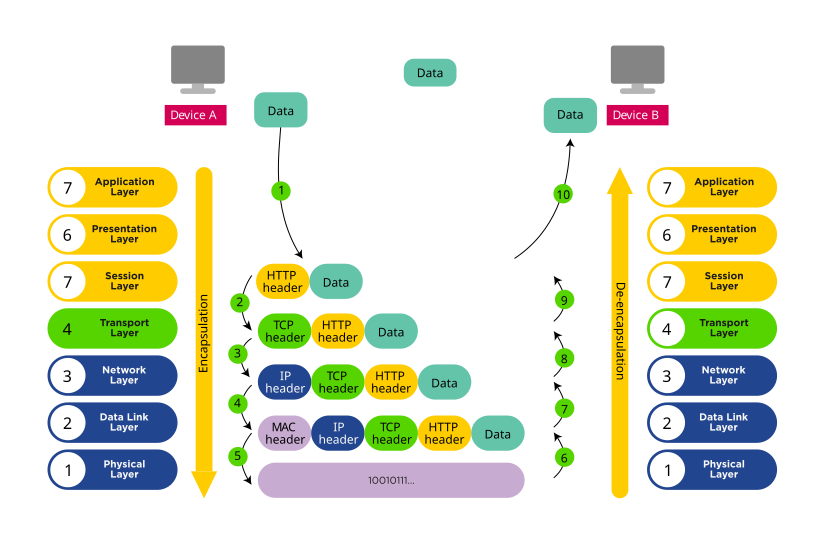
That’s the simplified version. DDoS attacks can be very complex and can be used to target different layers of something called the OSI (Open Systems Interconnection) model – a conceptual framework used to understand network interactions. The OSI model has seven layers that include:
| Layer 7: Application
Provides network services to applications; interface for end-user processes. Layer 6: Presentation Translates data between the network and application formats; handles encryption. Layer 5: Session Manages sessions between applications; sets up, manages, and terminates connections. Layer 4: Transport Ensures complete data transfer with error handling and flow control. Layer 3: Network Determines the physical path for data; handles packet routing. Layer 2: Data Link Provides node-to-node data transfer and error correction. Layer 1: Physical Transmits raw bit stream over the physical medium. |
|
The OSI model makes it easier to understand some of the stats flying around about DDoS attacks, such as CloudFlare observing a 10% decline in application layer DDoS attacks from Q2 to Q3 2022. But context is necessary, since DDoS attacks increased by 67% between 2021 and 2022.
And where online industries (e.g. eCommerce, travel, etc.) received the most application layer attacks, gaming and gambling companies were the most targeted by network-layer attacks with a 405% increase in attacks between Q2 and Q3 2022 thanks to the Mirai botnet.
How DDoS Attacks Are Executed
A botnet, such as Mirai, is a network of compromised internet-connected devices used to flood target systems or networks with traffic. There are generally three types of attacks, each corresponding to a different layer of the OSI model:
- Volume-based attacks: These include ICMP floods, UDP floods, and other spoofed-packet floods. The goal is to saturate the bandwidth of the attacked site.
- Protocol attacks: These include SYN floods, fragmented packet attacks, Ping of Death, etc. They consume actual server resources, or those of intermediate communication equipment, such as firewalls and load balancers.
- Application Layer attacks: Requests are made to the application layer, such as HTTP requests, which are the most debilitating as they look legitimate but intend to overwhelm the web server.
Regardless of the attack type, the typical format of a DDoS remains the same, and can be executed over days, months, or even years:
Creating the botnet
The process starts with attackers compromising vulnerable systems such as computers, mobile devices, and generally any IoT device, and installing malware. Infected systems are called ‘bots’, and can be controlled by the attacker without the owners’ knowledge.
Ready, set, attack!
Armed with a network of controllable bots, the attacker instructs each bot to send traffic to the target. This traffic can be legitimate, such as a username and password combination submitted to a login form.
The sheer number of bots sending the same traffic to the same destination typically overwhelms the target. However, where target systems or networks adapt to one form of attack, attackers may vary the form or destination of the attack.
Impact
The result is that the server, service, or network is overwhelmed and either responds so slowly that it’s unusable or crashes completely. Legitimate users cannot access the service, leading to downtime and potential financial and reputational damage.
Mitigating DDoS: What Can You Do?
Protecting a web server from DDoS attacks involves a combination of strategies, tools, and best practices aimed at mitigating the impact of such attacks. Here are some effective methods:
- Host securely: Choosing a host focused on DDoS prevention and mitigation can serve as a robust layer of protection for your network and servers. Choosing managed hosting takes that even one step further, since the host then typically also assumes responsibility for the security of your network and / or servers.
- Overprovisioning Bandwidth: More bandwidth capacity than you usually require can help absorb the increased traffic of a smaller DDoS attack. However, this alone isn’t sufficient for larger scale attacks.
- Rate Limiting: Configure your server or firewall to limit the number of requests a user can make within a certain period of time. This helps prevent your server from being overwhelmed by too many requests at once.
- Web Application Firewall (WAF): A WAF can be configured to monitor incoming traffic and block traffic that appears suspicious. It can help protect against SQL injection, cross-site scripting (XSS), and other types of application layer attacks which often accompany DDoS attempts.
- Content Delivery Network (CDN): A CDN can distribute your traffic across multiple, geographically dispersed servers. This not only speeds up content delivery but also helps to absorb and spread out any malicious traffic across a wider network, reducing strain on any single server.
- DDoS Protection Services: Many cloud-based services specialize in recognizing and mitigating DDoS attacks before they reach your server. Providers such as Cloudflare, Akamai, and AWS Shield offer such services, which can handle very large-scale attacks.
- Redundancy and Failover Systems: Implementing a failover system or redundant infrastructure can ensure service continuity even when one server or component is under attack. This is usually part of a broader disaster recovery and business continuity strategy.
- Regular Updates and Patch Management: Keep your server’s operating system and any installed software up to date with the latest patches. Security vulnerabilities in software can be exploited as part of a DDoS attack.
- Network Hardware: Investing in better quality network hardware that includes integrated hardware firewalls can also help filter out malicious traffic and recognize unusual traffic patterns.
- Monitoring and Alerts: Use monitoring tools to watch traffic and detect potential DDoS activity early. Automated alerts can help you respond to incidents before they escalate.
Each of these strategies can contribute significantly to your defenses against DDoS attacks, depending on the scale and complexity of your operations. Combining several approaches will usually provide the best protection.
As DDoS attacks evolve in complexity and intensity, understanding their fundamentals and the targeted layers of the OSI model becomes crucial for any cyber defense strategy. Proactive prevention, combined with robust mitigation techniques, can significantly reduce the risk and impact of these attacks. It is essential for organizations to stay vigilant, regularly update their security protocols, and employ a multi-layered defense approach to safeguard their digital landscapes. By doing so, they not only protect their own assets but also contribute to the overall health of the digital ecosystem, ensuring service continuity and reliability in an increasingly interconnected world.”